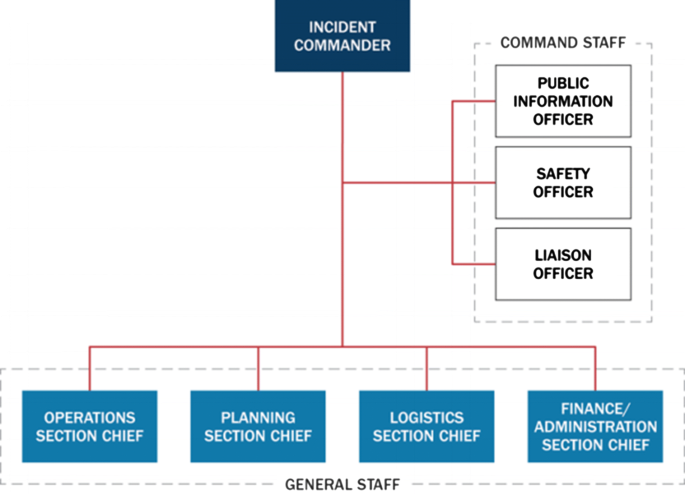
Table 2.1 from A Model Assessment Tool for the Incident Command System: A Case Study of the San Antonio Fire Department | Semantic Scholar
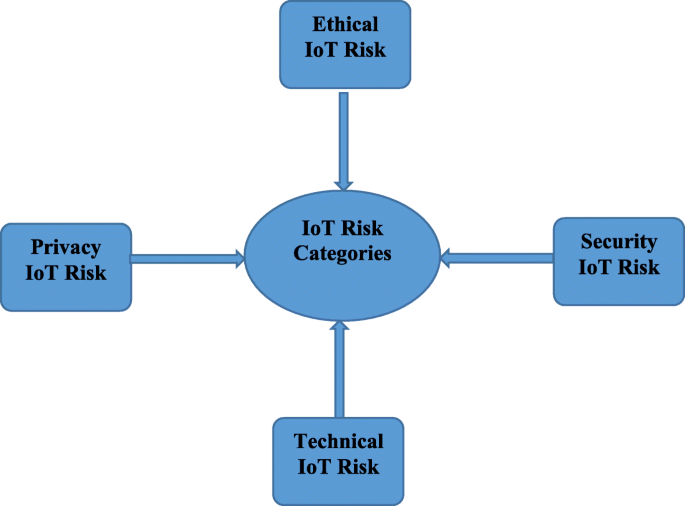
IoT cyber risk: a holistic analysis of cyber risk assessment frameworks, risk vectors, and risk ranking process | EURASIP Journal on Information Security | Full Text

An adaptive case management system to support integrated care services: Lessons learned from the NEXES project - ScienceDirect
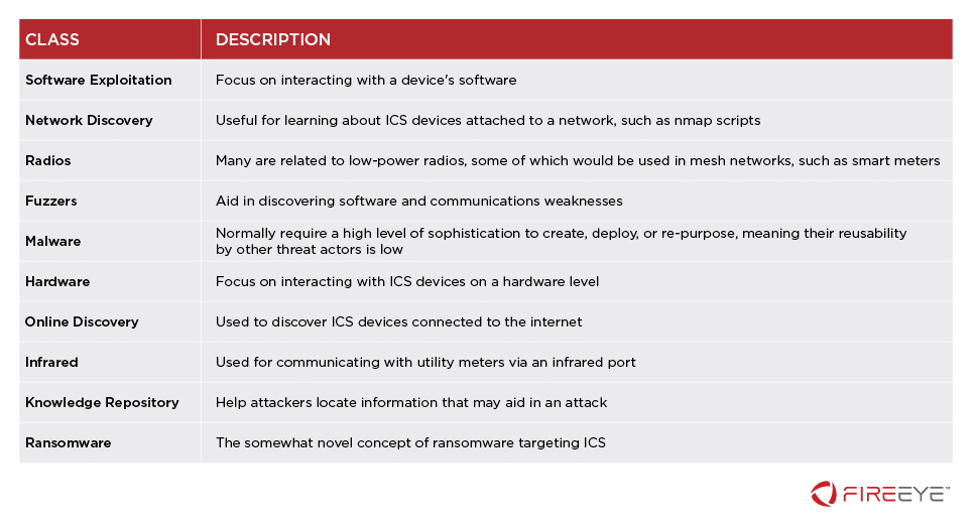
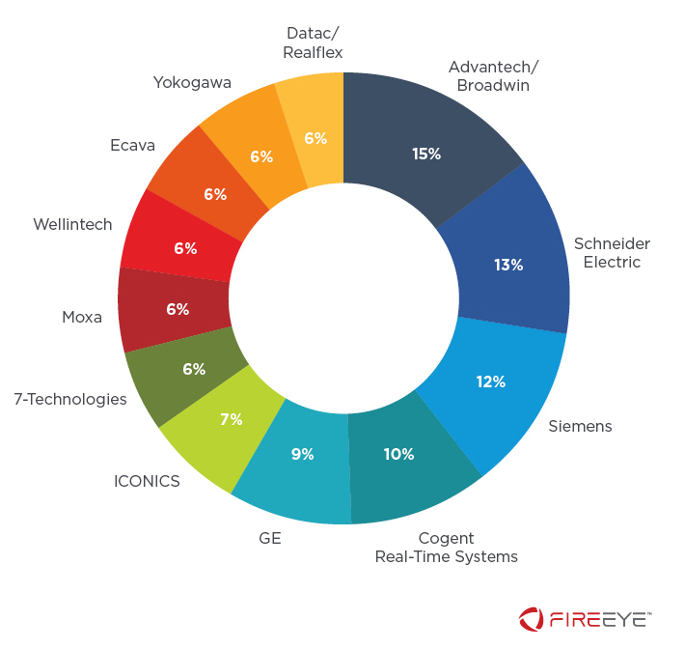
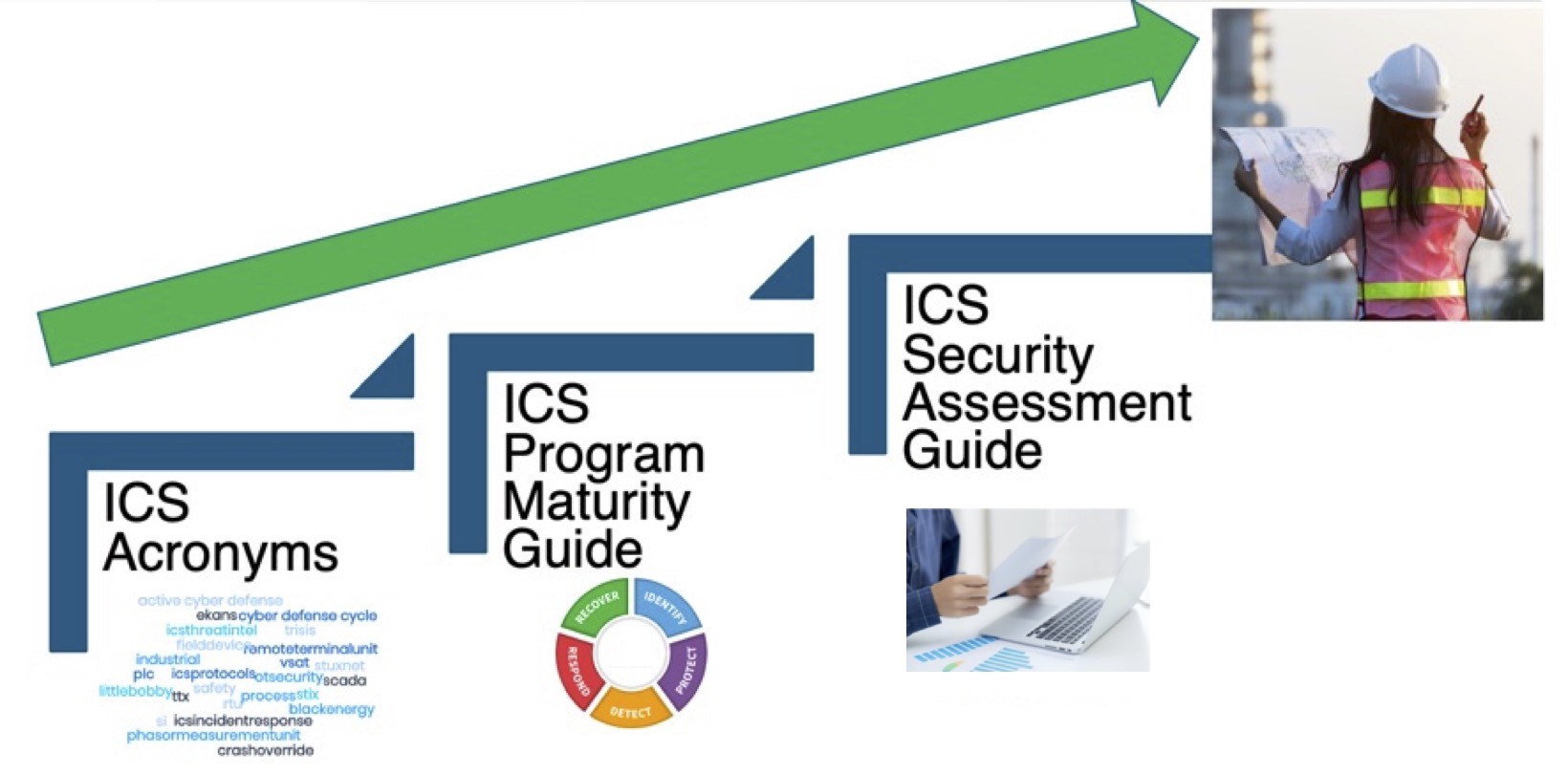
Monitoring ICS Cyber Operation Tools and Software Exploit Modules To Anticipate Future Threats | Mandiant
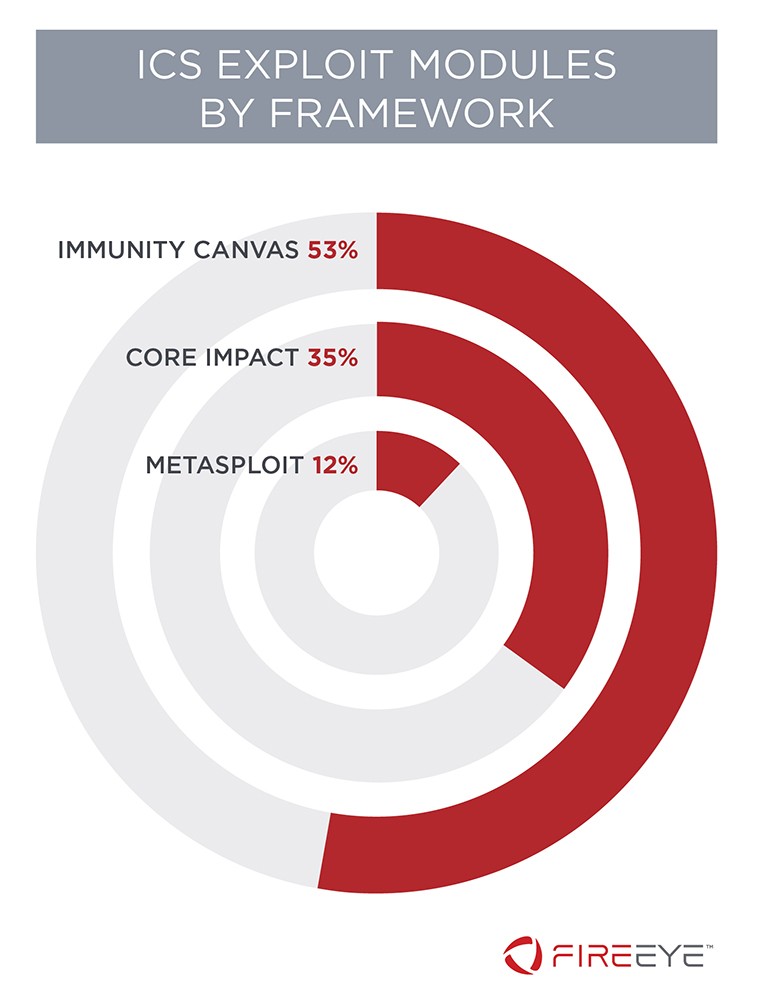
Monitoring ICS Cyber Operation Tools and Software Exploit Modules To Anticipate Future Threats | Mandiant
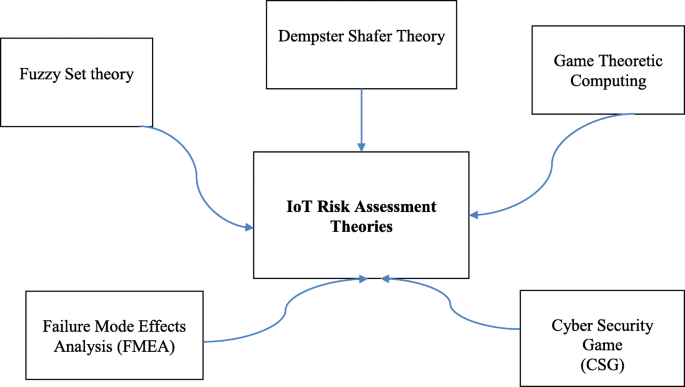
IoT cyber risk: a holistic analysis of cyber risk assessment frameworks, risk vectors, and risk ranking process | EURASIP Journal on Information Security | Full Text