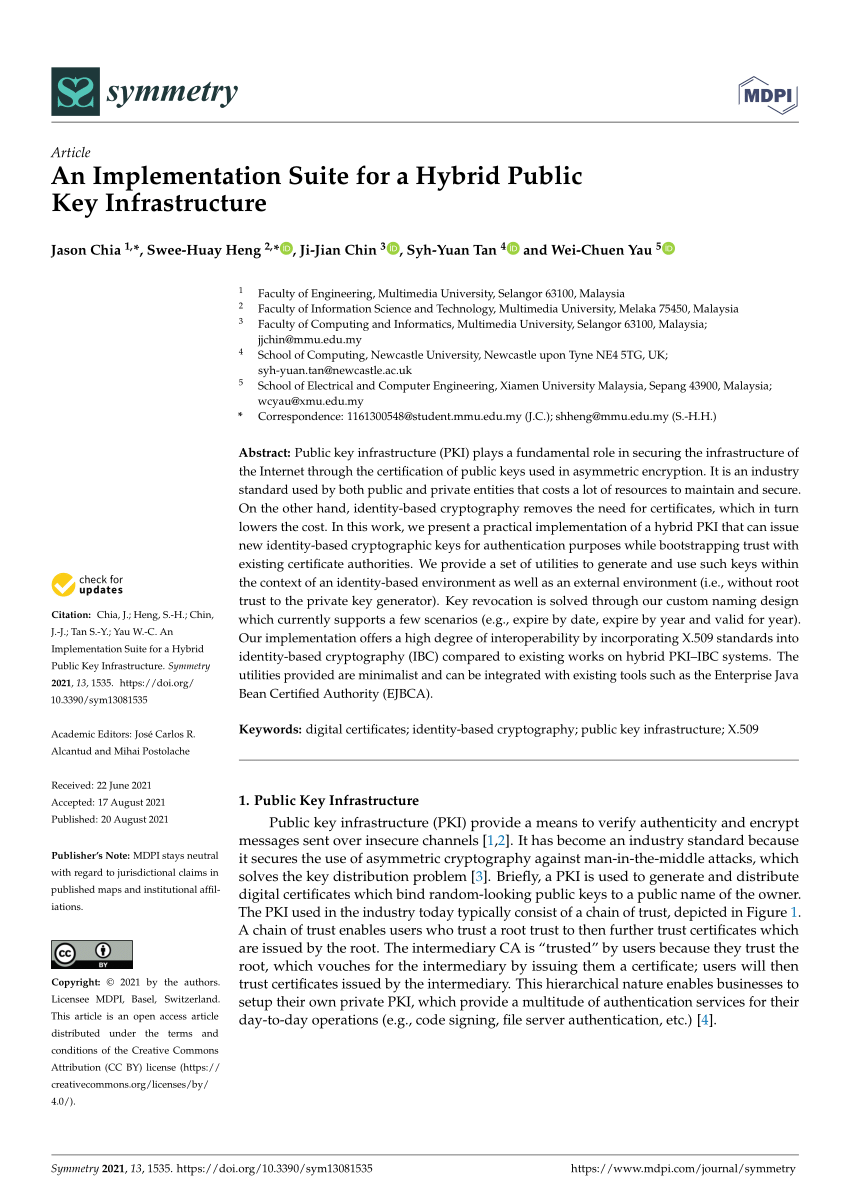
Offline phase (once). The key generator computes a (long) proving key... | Download Scientific Diagram
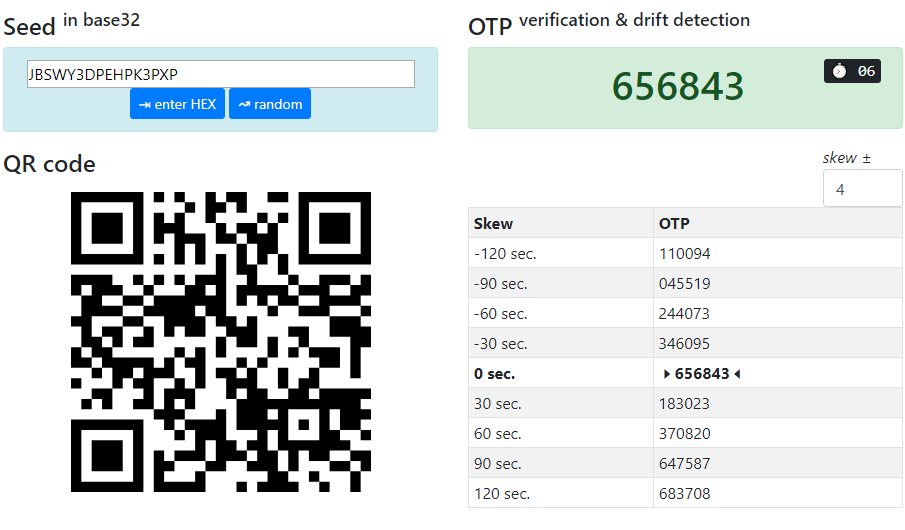
TOKEN2 Switzerland 🇨🇭 | TOTP Hardware tokens with ESET Secure Authentication | TOKEN2 MFA Products and Services | programmable hardware token, FIDO2 key, U2F key, TOTP, OATH-TOTP SHA-1 SHA-256 hardware tokens